Kiosk Breakouts - Restricted Environments To Complete Access
Kiosk Breakouts - Restricted Environments To Complete Access
Published 10/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 677.85 MB | Duration: 1h 37m
Hands-On How Red Teamers and Threat Actors (APT) Breakout Kiosk Enviroments in the Real World
What you'll learn
Kiosk Breakouts
Ethical Hacking
Cyber Security
Thinking outside the box
Nothing is secure
No System is safe
Requirements
A computer with 4GB ram to support 1 VM running
Basic understanding of operating systems
Strong will to learn & creative mindset
If you like Hands-On, well this is the course for you, we do Hands-On here
Description
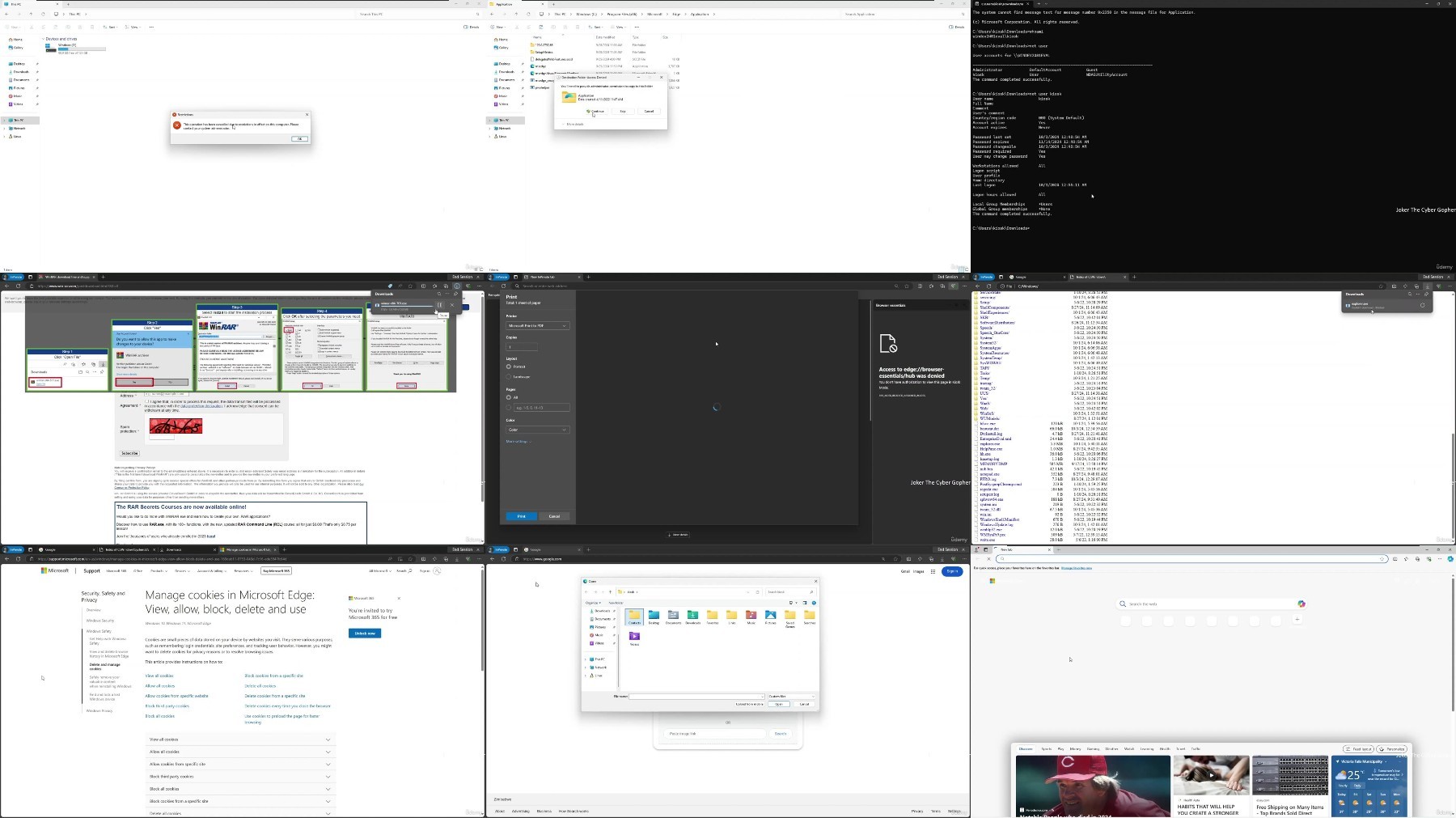
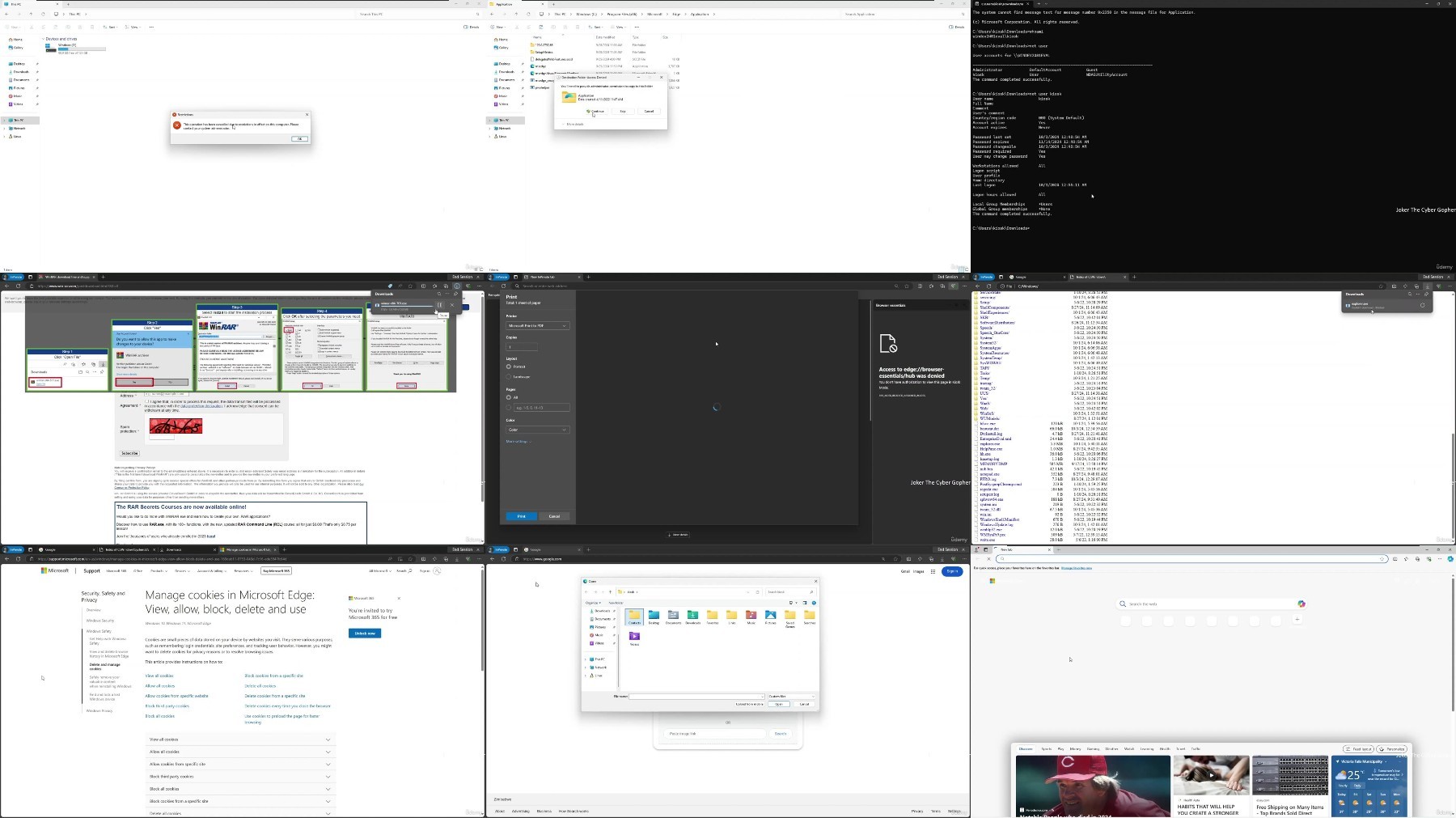
As public kiosks become more widespread in various industries, from retail to transportation, ensuring their security is critical. This course delves into kiosk breakouts—a technique used by attackers to escape the restricted environments of kiosks, such as ATMs, self-service terminals, and information kiosks, to gain unauthorized access to the underlying system. Understanding how these breakouts occur and, more importantly, how to prevent them is vital for maintaining secure public systems.In this course, participants will learn the different methods attackers use to exploit kiosk vulnerabilities, including bypassing operating system restrictions, escaping user interface sandboxes, exploiting browser vulnerabilities, and leveraging physical access. Students will also explore the defensive techniques used to mitigate these attacks, such as properly configuring kiosk modes, securing browsers, enforcing network access controls, and monitoring for suspicious activity.Hands-on labs will allow participants to engage directly with real-world scenarios, practicing how to secure kiosk systems, detect potential intrusions, and apply security measures to minimize risk. By studying both offensive and defensive tactics, learners will gain a holistic understanding of how to protect kiosks from emerging threats.By the end of the course, students will have developed the technical expertise to secure public kiosks against potential breakouts, making it ideal for cybersecurity professionals, IT administrators, and anyone tasked with managing or securing these systems. Graduates will be prepared to implement effective countermeasures to protect critical kiosk infrastructure.
Overview
Section 1: Course Prelude
Lecture 1 Introduction
Lecture 2 Intro To Kiosk Breakouts
Section 2: 2. Lab Setup & Configuration
Lecture 3 Welcome
Lecture 4 Installing VMware Pro
Lecture 5 Downloading Kali & Windows 11 VM
Lecture 6 Setting Up Machines On VMware
Lecture 7 Getting Windows 11 VM Ready
Section 3: 3. Kiosk Breaking Outs
Lecture 8 Bulidng Kiosk Environment - Easy Mode
Lecture 9 Kiosk Breakout - Easy Mode
Lecture 10 Bulidng Kiosk Environment - Hard Mode
Lecture 11 Keep In Mind
Lecture 12 Kiosk Breakout - Hard Mode
Section 4: 4. Wrap Up
Lecture 13 Wrap Up
Red Teamers - Leveling their skills in their world of compromising systems & evading security mechanism,Blue Teamer - Learn how threat actors work or move in the wild, so they can defend better, protect their systems and educate their fellow workers for better security,Any-One - Off course, anyone in the Cyber Security field who just wanna learn or know how threat actors act in the wild
https://ddownload.com/q0miml6fp45e/.Kiosk.Breakouts.-.Restricted.Environments.to.Complete.Access.rar
What you'll learn
Kiosk Breakouts
Ethical Hacking
Cyber Security
Thinking outside the box
Nothing is secure
No System is safe
Requirements
A computer with 4GB ram to support 1 VM running
Basic understanding of operating systems
Strong will to learn & creative mindset
If you like Hands-On, well this is the course for you, we do Hands-On here
Description
As public kiosks become more widespread in various industries, from retail to transportation, ensuring their security is critical. This course delves into kiosk breakouts—a technique used by attackers to escape the restricted environments of kiosks, such as ATMs, self-service terminals, and information kiosks, to gain unauthorized access to the underlying system. Understanding how these breakouts occur and, more importantly, how to prevent them is vital for maintaining secure public systems.In this course, participants will learn the different methods attackers use to exploit kiosk vulnerabilities, including bypassing operating system restrictions, escaping user interface sandboxes, exploiting browser vulnerabilities, and leveraging physical access. Students will also explore the defensive techniques used to mitigate these attacks, such as properly configuring kiosk modes, securing browsers, enforcing network access controls, and monitoring for suspicious activity.Hands-on labs will allow participants to engage directly with real-world scenarios, practicing how to secure kiosk systems, detect potential intrusions, and apply security measures to minimize risk. By studying both offensive and defensive tactics, learners will gain a holistic understanding of how to protect kiosks from emerging threats.By the end of the course, students will have developed the technical expertise to secure public kiosks against potential breakouts, making it ideal for cybersecurity professionals, IT administrators, and anyone tasked with managing or securing these systems. Graduates will be prepared to implement effective countermeasures to protect critical kiosk infrastructure.
Overview
Section 1: Course Prelude
Lecture 1 Introduction
Lecture 2 Intro To Kiosk Breakouts
Section 2: 2. Lab Setup & Configuration
Lecture 3 Welcome
Lecture 4 Installing VMware Pro
Lecture 5 Downloading Kali & Windows 11 VM
Lecture 6 Setting Up Machines On VMware
Lecture 7 Getting Windows 11 VM Ready
Section 3: 3. Kiosk Breaking Outs
Lecture 8 Bulidng Kiosk Environment - Easy Mode
Lecture 9 Kiosk Breakout - Easy Mode
Lecture 10 Bulidng Kiosk Environment - Hard Mode
Lecture 11 Keep In Mind
Lecture 12 Kiosk Breakout - Hard Mode
Section 4: 4. Wrap Up
Lecture 13 Wrap Up
Red Teamers - Leveling their skills in their world of compromising systems & evading security mechanism,Blue Teamer - Learn how threat actors work or move in the wild, so they can defend better, protect their systems and educate their fellow workers for better security,Any-One - Off course, anyone in the Cyber Security field who just wanna learn or know how threat actors act in the wild
https://ddownload.com/q0miml6fp45e/.Kiosk.Breakouts.-.Restricted.Environments.to.Complete.Access.rar